PKI Tutorials - Herong's Tutorial Examples - v2.32, by Herong Yang
HTTPS Communication Data Encryption
This section describes the HTTPS communication data encryption process - Browser generates an encryption key, encrypts it using server public key and sends it to the server; Browser encrypts data with the encryption key; Server encrypts return data with the same encryption key.
As mentioned earlier, communication encryption is also an important process to ensure the security of the HTTPS communication. The following diagram from snapblox.com shows how HTTPS communication encryption is done at a high level:
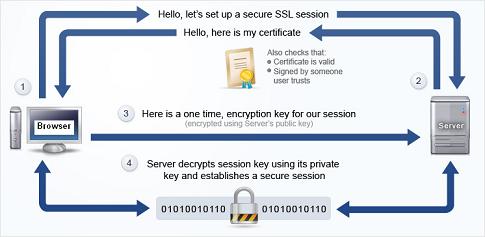
As you can see from the diagram, after it is done with the Web server authentication process (Step 1 and 2 in the diagram), the browser starts the communication encryption process with these activities:
Generating and delivering an encryption key (Step 3 in the diagram):
- The browser generates a one-time encryption key using a secret key algorithm.
- The browser encrypts the encryption key (secret key) with the public key embedded in the server certificate.
- The browser sends the encrypted encryption key to the server over the Internet.
- The server decrypts the encryption key with the server private key.
Sending and receiving encrypted data (Step 4 in the diagram):
- The browser encrypts data to be sent to the server with the encryption key.
- The browser sends encrypted data to the server over the Internet.
- The server decrypts data with the encryption key received earlier from the browser.
- The server encrypts return data with the same encryption key.
- The browser receives encrypted return data from the server.
- The browser decrypts return data with the same encryption key.
The goal of HTTPS communication encryption is to build a protection on data exchanged between the browser and the server. The protected data will travel through many other systems between your browser and the server. But no other system can see the content of the data because the data is encrypted.
Can you really trust the HTTPS communication encryption? Yes, you can, if following assumptions are true:
- You trust the strength of the public key encryption algorithm used to encrypt and delivery the encryption key.
- You trust the server not leaking the encryption key to other systems.
- You trust the strength of the secret key algorithm used to encrypt data sent to and receive from the server.
Table of Contents
Introduction of PKI (Public Key Infrastructure)
►Introduction of HTTPS (Hypertext Transfer Protocol Secure)
What Is HTTPS (Hypertext Transfer Protocol Secure)?
HTTPS Server Authentication Process
►HTTPS Communication Data Encryption
Using HTTPS with Google Chrome
Using HTTPS with Mozilla Firefox
HTTPS with IE (Internet Explorer)
Android and Server Certificate
Windows Certificate Stores and Console
RDP (Remote Desktop Protocol) and Server Certificate
macOS Certificate Stores and Keychain Access
Perl Scripts Communicating with HTTPS Servers
PHP Scripts Communicating with HTTPS Servers
Java Programs Communicating with HTTPS Servers
.NET Programs Communicating with HTTPS Servers
CAcert.org - Root CA Offering Free Certificates
PKI CA Administration - Issuing Certificates
Comodo Free Personal Certificate
Digital Signature - Microsoft Word
Digital Signature - OpenOffice.org 3