PKI Tutorials - Herong's Tutorial Examples - v2.32, by Herong Yang
What Is PKI (Public Key Infrastructure)
This section describes what is PKI (Public Key Infrastructure) - an information technology infrastructure that enables Internet users to securely exchange information using the public and private key technology.
What Is PKI (Public Key Infrastructure)? PKI is an information technology infrastructure that enables Internet users to securely and privately exchange information through the use of a public and a private key pair that is obtained and shared through a trusted authority. The public key infrastructure provides for a digital certificate that can identify an individual or an organization and directory services that can store and, when necessary, revoke the certificates.
Elements of a public key infrastructure are:
- A public and private key encryption technology that can be used to encrypt and decrypt information.
- Subjects (users, organizations, or systems) who wants to use the public and private key technology to exchange information securely.
- A registration authority (RA) that verifies subject's identity.
- A certificate authority (CA) that issues the digital certificate binding subject's identity with subject's public key.
- A validation authority (VA) that verifies the digital certificate of a subject.
- A certificate revocation list (CRL) that contains certificates revoked by the CA.
The following diagram from wikipedia.org provides a good illustration of how PKI works:
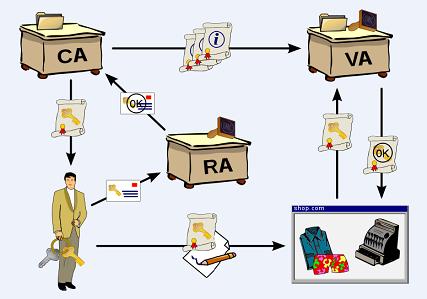
Rough outline of diagram: A user applies for a certificate with his public key at a registration authority (RA). The latter confirms the user's identity to the certification authority (CA) which in turn issues the certificate. The user can then digitally sign a contract using his new certificate. His identity is then checked by the contracting party with a validation authority (VA) which again receives information about issued certificates by the certification authority.
Table of Contents
►Introduction of PKI (Public Key Infrastructure)
►What Is PKI (Public Key Infrastructure)
Usage Examples of Public Key Infrastructure
Most Popular Certificate Authorities
Introduction of HTTPS (Hypertext Transfer Protocol Secure)
Using HTTPS with Google Chrome
Using HTTPS with Mozilla Firefox
HTTPS with IE (Internet Explorer)
Android and Server Certificate
Windows Certificate Stores and Console
RDP (Remote Desktop Protocol) and Server Certificate
macOS Certificate Stores and Keychain Access
Perl Scripts Communicating with HTTPS Servers
PHP Scripts Communicating with HTTPS Servers
Java Programs Communicating with HTTPS Servers
.NET Programs Communicating with HTTPS Servers
CAcert.org - Root CA Offering Free Certificates
PKI CA Administration - Issuing Certificates
Comodo Free Personal Certificate
Digital Signature - Microsoft Word
Digital Signature - OpenOffice.org 3