Windows Tutorials - Herong's Tutorial Examples - v5.62, by Dr. Herong Yang
Winsock 2 LSP and Spyware Trojans
This section describes how the Winsock 2 LSP stack can be exploited by spyware trojans to relink existing or adding new LSP registry entries.
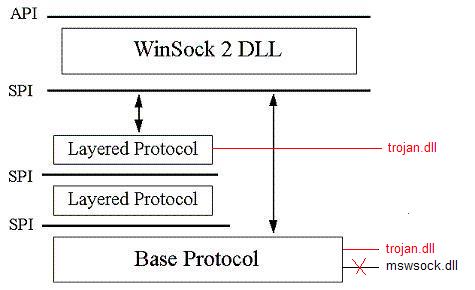
As you can see from the Winsock SPI and LSP design, Internet spyware and trojans can easily exploit the following areas:
1. Modifying Winsock 2 LSP stack settings to run trojan DLL files instead of Windows system files: rsvpsp.dll and mswsock.dll.
2. Adding extra entries in the Winsock 2 LSP stack to run trojan DLL files.
Once a spyware trojan DLL file gets installed into the Winsock 2 LSP stack through one of the above methods, it will quietly filtering all Internet communications going out of and coming into the system and:
- To collect user name and password information you entered to log into your online accounts, known as PWS (PassWord Stealer) trajons.
- To collect email addresses or websites you have used while visiting websites.
- To send collected information to the information stealer.
The diagram shows how a spyware trojan DLL can be installed into the Winsock 2 LSP stack:
A simple way to detect spyware trojan infections in Winsock 2 LSP stack is to use the "netsh winsock show catalog" command as presented in the previous section. You need to inspect all DLL files reported by the command and find who is a trojan DLL.
Table of Contents
Introduction to Microsoft Windows
Introduction to Windows Explorer
Introduction to Internet Explorer
"Paint" Program and Computer Graphics
GIMP - GNU Image Manipulation Program
JPEG Image File Format Quality and Size
GIF Image File Format and Transparent Background
"WinZip" - ZIP File Compression Tool
"WinRAR" - RAR and ZIP File Compression Tool
FTP Server, Client and Commands
"FileZilla" - Free FTP Client and Server
Web Server Log Files and Analysis Tool - "Analog"
Spyware Adware Detection and Removal
IE Addon Program Listing and Removal
Vundo (VirtuMonde/VirtuMundo) - vtsts.dll Removal
Trojan and Malware "Puper" Description and Removal
VSToolbar (VSAdd-in.dll) - Description and Removal
Spybot - Spyware Blocker, Detection and Removal
Setting Up and Using Crossover Cable Network
Home Network Gateway - DSL Modem/Wireless Router
Windows Task Manager - The System Performance Tool
"tasklist" Command Line Tool to List Process Information
"msconfig" - System Configuration Tool
Configuring and Managing System Services
Windows Registry Key and Value Management Tools
Startup Programs Removal for Better System Performance
►Winsock - Windows Sockets API
What is Winsock (Windows Socket) API
mswsock.dll - Microsoft Windows Sockets 2.0 Service Provider
"netsh winsock show catalog" - Showing Winsock 2 LSP
►Winsock 2 LSP and Spyware Trojans
rundlll.dll - Winsock 2 LSP Spyware Trojan
Winsock 2 LSP Stack Registry Corruption